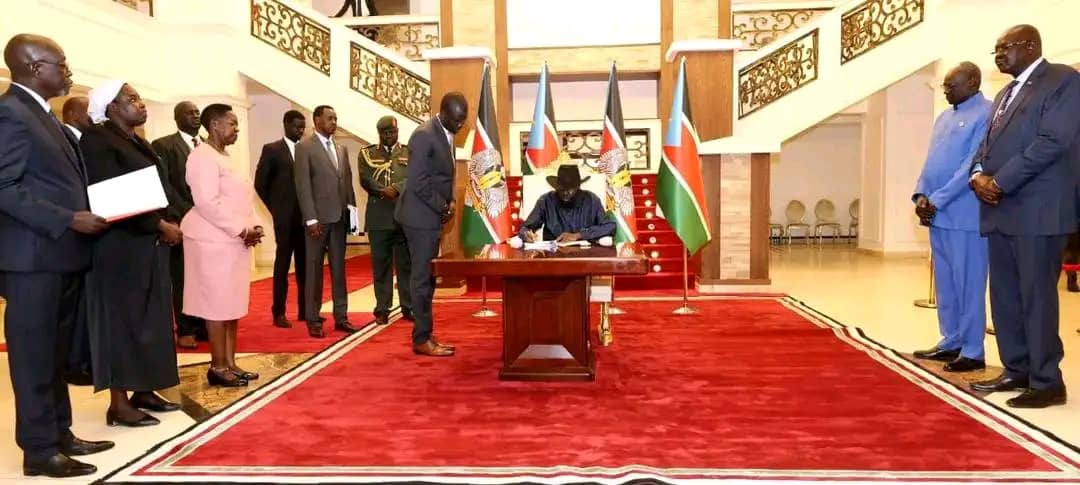
In a world where our lives are stored in the cloud and our economies run on code, what happens when the law finally catches up? For South Sudan, that moment arrived on February 8th, 2026, when President Salva Kiir Mayardit signed into law “The Cybercrimes and Computer Misuse Act, 2026.” This isn’t just a collection of rules; the Act draws a digital line in the sand regarding social cohesion and national integrity. From a legal tech policy perspective, this is a watershed moment that moves South Sudan from a digital “Wild West” into a highly regulated frontier.
For citizens, entrepreneurs, and global observers, the Act is a complex weave of security and restriction. Here are the seven most impactful takeaways you need to understand.
1. Justice Without Borders: Extraterritorial Jurisdiction
The internet has no borders, and now, neither does South Sudanese digital law. Under Section 7, the state asserts its right to prosecute cyber-criminals regardless of where the keyboard is located. The criteria for this jurisdiction are broad: the law applies if the crime involves a ship or aircraft registered in South Sudan, if the victim is a citizen, or—most significantly for international investigations—under Section 7(d), if the preparation, planning, direction, or funding occurred within the Republic, even if the crime itself was executed abroad.
The Act is explicit about its global reach, stating it applies:
“…irrespective of his or her nationality, citizenship or location.” (Section 7)
This suggests that South Sudan is positioning itself as an active participant in global digital policing, targeting the financial and logistical pipelines of cybercrime.
2. The 180-Day Memory: Service Provider Obligations
Under Section 6, internet and data service providers are now the “first responders” of data retention. They are mandated to keep, store, and record specific information for a continuous period of 180 days. This includes user identification, traffic data (origin and destination), and data related to peripheral devices.
From a digital rights perspective, however, the “So what?” factor lies in the tension between surveillance and secrecy. While the retention mandate is heavy, Section 6(1)(d) offers a vital legal shield: providers must maintain confidentiality and are prohibited from disclosing this saved data without an order from a “competent judicial authority.” This ensures that while the “memory” of the network is long, it is not—theoretically—an open book for every official without a warrant.
3. Defining the “Undesirable”: Content Moderation & Social Values
The Act takes an aggressive stance on social cohesion. Section 42 mandates that online administrators remove “undesirable content” within a prescribed period after receiving notice. The grounds for removal are specific and politically sensitive, including “Tribalism,” “Gender discrimination,” and “promoting racism.”
The real challenge for digital rights lies in Section 5, which defines “Indecent Content” as anything “contrary to the norms and traditions” of the country. For a journalist, this is a red flag: who defines these “norms”? In a diverse society, tethering legal definitions to subjective cultural traditions creates a high risk for inconsistent or selective enforcement, potentially chilling free expression under the guise of protecting values.
4. When Your Computer Becomes “Critical National Infrastructure”
Chapter V introduces a heavy burden for the private sector. Under Section 26, the “Competent Minister” (defined in Section 5 as the Minister responsible for communication) can designate private computer systems as Critical National Infrastructure (CNI). This applies if the system is deemed essential for national security or the economic well-being of citizens, specifically targeting banking and financial services, public utilities, and public transportation (Section 26(3)(c)).
Once your business is designated as CNI, you are no longer just a private entity; you are a guardian of the state. Under Section 30, owners must report any cybersecurity incident within twenty-four hours of detection. Failure to comply can lead to administrative penalties prescribed by the Minister, turning cybersecurity from a “best practice” into a high-stakes legal obligation.
5. The High Cost of Interference: Heavy Penalties
The financial and physical stakes of the Act are staggering. Section 39, regarding “Unauthorised Interference,” sets a massive penalty for those who hinder computer systems in a way that threatens public health or safety: a fine of up to seventy-five million South Sudan pounds, ten years in prison, or both.
A keen legal analyst will notice the severity of the terrorism provisions. Section 31(3)(b) allows for a 25-year imprisonment term for acts against CNI that are deemed “terrorist acts.” Interestingly, this contrasts with Section 56, which sets a limit of 20 years for general cyberterrorism. This discrepancy highlights that the state views an attack on its infrastructure as even more dangerous than general digital terror.
6. New Legal Shields Against Modern Harassment
The Act finally provides a shield for victims of modern digital abuse, bringing South Sudanese law into the 21st century.
- Revenge Pornography (Section 49): It is now a crime to publish intimate images without consent with the intent to cause distress.
- Cyberbullying (Section 53): The law targets “repeated and intentional” use of technology to harass, threaten, or target individuals.
- Cybersquatting (Section 54): In a win for local brands, it is now illegal to intentionally use another person’s name, trademark, or domain name without consent. This specific inclusion of domain names is vital for protecting the nation’s burgeoning digital economy from bad actors looking to ransom business identities.
7. “Spontaneous Information”: International Cooperation
Cybercrime is rarely local, and Section 10 introduces a proactive approach to global policing known as “Spontaneous Information.” The Authority can now forward information from a domestic investigation to a foreign state without a prior request, provided it assists in cybercrime proceedings. As the Act states:
“The Authority may… forward to a foreign State information obtained within the framework of a South Sudan investigation where it considers that the disclosure of such information may assist the foreign State…” (Section 10)
This signals that South Sudan intends to be a “loud” partner in international law enforcement, though the Authority may refuse if the foreign state doesn’t commit to confidentiality conditions.
Conclusion: A New Chapter for South Sudanese Cyberspace
The “Cybercrimes and Computer Misuse Act, 2026” fundamentally reconfigures the nation’s digital architecture. Beyond the penalties, it establishes the National Cybercrime Prosecution Unit (under the Ministry of Justice) to lead investigations and the SS-CIRT/CC (South Sudan Computer Incident Response Team Coordination Centre). Per Section 32(2), the SS-CIRT/CC will serve as the nation’s technical “focal point,” providing the critical analysis needed to defend against emerging threats.
As South Sudan steps into this new era of digital regulation, we must ask: How will the balance between national security and individual digital freedom evolve as these broadly defined “norms and traditions” meet the reality of an open, global internet?
